Hello,
Has anybody got ShinyProxy to work with EKS? The ShinyProxy I have won’t launch new containers and I just wanted to know if this is possible and if it is, can anybody share their app settings please?
Thanks!
Hi Mark,
We have several different environments/deployments running on AWS EKS currently. Everything works quite well so far.
To what extent did you follow https://github.com/openanalytics/shinyproxy-config-examples/tree/master/03-containerized-kubernetes?
Please note that if you use containers that are stored in a private repository, you need to make sure to add an image-pull-secret to shinyproxy/application.yml. https://www.shinyproxy.io/configuration/ also contains extra information in the ‘Kubernetes’ paragraph.
Happy to have a glance at your yaml files.
Best,
Michael
I thought I did copied it exactly. I have torn down my cluster and I am going to start again.
What is your apiGroup ? Is it meant to be rbac.authorization.k8s.io ?
Thanks
Mark
I’ve followed the guide but this time I put built the docker container on each node and it is working. hurray!
I was using ECR before. I am going to try and use ECR again following your advice. I would have thought the nodes could have pulled from ECR using the node’s IAM role?
We have been using DockerHub where I followed the Kubernetes documentation on secrets to create the proper secret (and then refer to it through ShinyProxy’s .yaml following the links I shared above). Not sure about ECR, but the documentation seems to agree with you https://docs.aws.amazon.com/eks/latest/userguide/managing-auth.html. Also note the ECR section here https://kubernetes.io/docs/concepts/containers/images/.
As a minor comment, I have created a similar ShinyProxy Kubernetes deployment on Google Cloud Platform through Kubernetes Engine, if you use their container registry you do not have to create a secret or something equivalent to an IAM role as long as your container registry and deployment are in the same project.
Best regards,
Michael
Hi Michael!
Could you please tell a bit in more details how did you setup Shinyproxy through Kubernetes Engine?
I would like to try that too.
Best regards,
Anatoly
Hi Anatoly,
The first step is to setup a cluster via the google cloud console using Kubernetes Engine. Once that cluster is up and running you can follow https://github.com/openanalytics/shinyproxy-config-examples/tree/master/03-containerized-kubernetes until you have a working demo setup based on those files. I can provide more detailed steps once I have a bit more time. Do you have prior experience with Kubernetes @Anatoliy_Vuets?
Best regards,
Michael
Michael, thank you for your reply!
“Do you have prior experience with Kubernetes” - not much: I played with deploying containerized apps in Kubernetes Engine but have no experience with custom Kubernetes deployments.
The tutorial for containerized ShinyProxy seems to be for custom Kubernetes deployments and not adopted for cloud deployments with their infrastructure (or maybe I’m missing something) so I have questions here…
How can I use container registry here? Should my app (Shiny app) images sit there?
In Kubernetes engine you typically put your app container in image registry and make its deployment in your cluster. Also you can add nice features like auto-scaling and benefit from rolling update if you want to update your app without restarting everything. How does these work with ShinyProxy?
Also from the tutorial “Ensure the kube-proxy-sidecar image is available on all your kube nodes. E.g. by repeating the above steps on all nodes.” - what do I do if I decide to increase the number of nodes in my cluster? How does it work with auto-scaling?
Sorry if some questions are dumb, this is because I have no much experience.
I’m a bit lost here.
Best regards,
Anatoly
Hi @Anatoliy_Vuets,
Your focus should initially be on shinyproxy-config-example/03-containerized-kubernetes/shinyproxy-example/application.yml. This yml file shows two applications 01_hello and 06_tabsets. I suggest you first leave this as it is and try to get ShinyProxy to work on Kubernetes. Once you have everything working, feel free to change the image names there to that of your own (this involves building the ShinyProxy image again and pushing it to your a container registry + modifying “shinyproxy-example” in spec.containers.name sp-deployment.yaml).
The deployment should be a few steps: start a Kubernetes cluster with Kubernetes Engine and then run kubectl create -f sp-deployment.yaml, sp-authorization.yaml and sp-service.yaml.
How can I use container registry here?
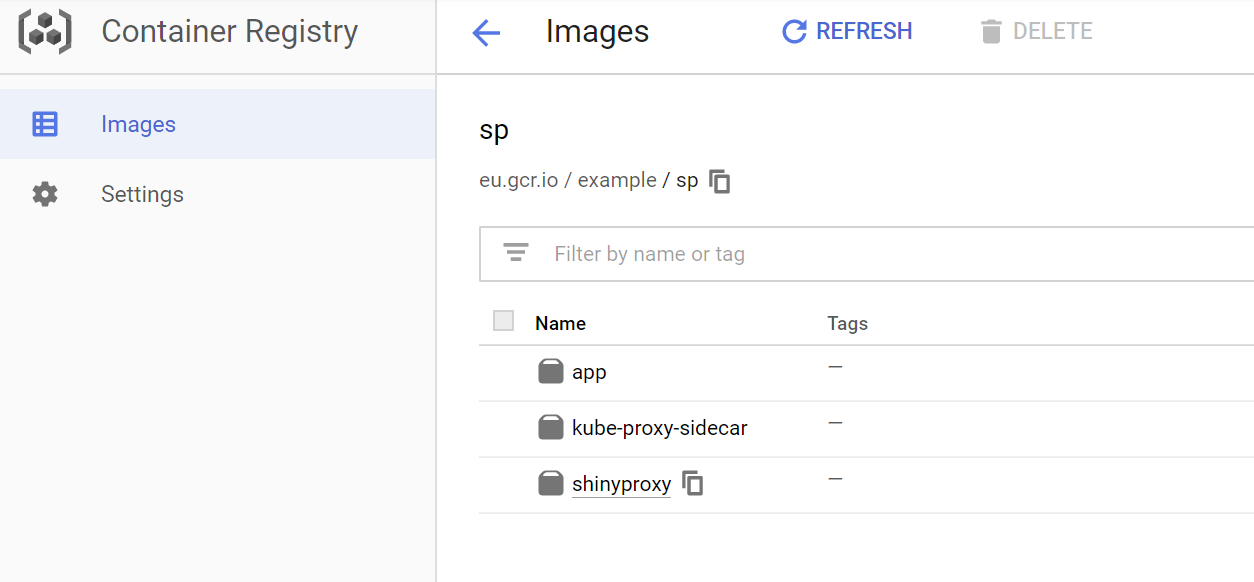
On GCS you can use Container Registry, if you use your own private images the sp-deployment.yaml and application.yml should use the path you see in the image below (Google Cloud console…). I recommend you first leave the files on GitHub as they are and try to get ShinyProxy working on Kubernetes with the demo applications.
Should my app (Shiny app) images sit there?
You should have a ShinyProxy image in a registry as well as images (which are specified in your ShinyProxy application.yaml file) that contain your Shiny applications. If I remember correctly, using Kubernetes Engine and Container Registry within the same Google Cloud project allows you to not have to be bothered with secrets to specify registry credentials.
Autoscaling
I may come back on that once I have more experience with our autoscaling setup on AWS EKS, we have it setup but it has not been tested thoroughly.
HI, @michaelhogersosis .
Can you a clarify a process of deployment?
Cause I’m stacked in step where I run ‘kubectl create -f sp-deployment.yaml’
Created workloads told me about failure when node going to container registry and try to pull example image. (GCR and Kluster on one project)
I saw some information about creating secret key for container registry, but I’m understood where use it in sp-deployment.yaml.
Thanks in advance.
PS. I’m trying to pull docker image on each node (like it describe in guide for kubernetes section 03-containerized-kubernetes) but deployment failure too.
Hi @mark, @Anatoliy_Vuets, @michaelhogersosis
I found solution for GCP, but it need edit basic instruction for 03-containerized-kubernetes
first of all we are need to authenticating in GSR in terminal you need connect to cluster with command
gcloud container clusters get-credentials shiny --zone us-central1-c --project your-project
then going to IAM create json key for GCR (google container registry) then in terminal type command:
create secret key for GCR
sudo kubectl create secret docker-registry gcr-json-key
–docker-server=gcr.io
–docker-username=_json_key
–docker-password="$(cat gcr.json)"
--docker-email=any-valid-email@host.com
will execute the command
patch default serviceaccount
sudo kubectl patch serviceaccount default
-p ‘{“imagePullSecrets”: [{“name”: “gcr-json-key”}]}’
after that for avoid pulling images to each node in cluster need to modify
apiVersion: apps/v1
kind: Deployment
metadata:
name: shinyproxy
spec:
selector:
matchLabels:
run: shinyproxy
replicas: 1
template:
metadata:
labels:
run: shinyproxy
spec:
** imagePullSecrets:**
** - name: gcr-json-key**
containers:
- name: shinyproxy
image: gcr.io/your-project/shinyproxy-example
imagePullPolicy: Always
ports:
- containerPort: 8080
- name: kube-proxy-sidecar
image: gcr.io/your-project/kube-proxy-sidecar
imagePullPolicy: Always
ports:
- containerPort: 8001
and it worked
I am confused on the image creation stage, my image looks like:
FROM docker.io/openanalytics/r-base:4.0.5
system libraries of general use
RUN apt-get update && apt-get install -y
sudo
pandoc
pandoc-citeproc
libcurl4-gnutls-dev
libcairo2-dev
libxt-dev
libssl-dev
libssh2-1-dev
libssl1.1
libpq-dev
libxml2-dev
&& rm -rf /var/lib/apt/lists/*
RUN mkdir /root/dps
COPY dps /root/dps
COPY application.yml /opt/shinyproxy/application.yml
EXPOSE 3838
CMD [“R”, “-e”, “shiny::runApp(’/root/dps’, port=3838)”]